What is AD&POP BLOCK browser plugin? — Fix Guide

Daniel Foster
Updated on April 27, 2026
AD&POP BLOCK – What is it?
“AD&POP BLOCK” search hijacker is a potentially unwanted application (PUA)1, that is promoted as a plugin for your internet browser. It is typically advertised as an add-on for Chrome or Firefox, that aids to browse some precise details, for instance, about sporting activity events, make your browser far more secure, enable downloading of any type of video clip, et cetera. Also, this app adds the “Managed by your organization” feature (on Chrome browsers).
Nevertheless, the “AD&POP BLOCK” plugin is quite ineffective because all such functions are currently integrated to your web browser and/or Windows. Such advertising and marketing slogans are targeted at low-skilled computer users, for example, pensioners or schoolchildren. But sometimes even professional users are getting caught on such an appeal. In specific situations, this hijacker is dispersed together with free tools.
AD&POP BLOCK Search Hijacker
| NAME | AD&POP BLOCK |
| Site | 1stepdownload.com |
| Hosting | AS13335 Cloudflare, Inc. United States, San Francisco |
| Infection Type | Browser Hijacker, Unwanted Application |
| IP Address | 104.21.11.239 |
| Symptoms | Changed search engine; search queries redirection |
| Similar behavior | Bing, Newtaber, Search |
| Fix Tool | GridinSoft Anti-MalwareTo remove possible virus infections, try to scan your PC |
How harmful is AD&POP BLOCK hijacker?
Besides its impracticality, AD&POP BLOCK hijacker is also quite hazardous for web browser utilization. It alters your search engine to its particular – 1stepdownload.com, and likewise transforms your background, adding its watermark on your background image (or, occasionally, changing it to default with the mentioned sign).
Aside from aesthetic changes done by AD&POP BLOCK hijacker, you might discover that some of your search questions are redirecting to the dubious sites, full of web links and promotions – so-called doorway sites. Such websites can consist of web links for malware downloads. The chance of redirecting rises if you attempt to start Google search page by force.
But all these actions are a lot more irritating than really harmful. The main hazard, particularly for people who have a great deal of secret information in their web browsers, is embedded in data collecting functionalities. Cookie files, chats, often-visited web pages, as well as various other activities are easily gathered by AD&POP BLOCK hijacker.
How to remove AD&POP BLOCK search hijacker?
- Download and install GridinSoft Anti-Malware.
- Open GridinSoft Anti-Malware and perform a “Standard scan“.
- “Move to quarantine” all items.
- Open “Tools” tab – Press “Reset Browser Settings“.
- Select proper browser and options – Click “Reset”.
- Restart your computer.
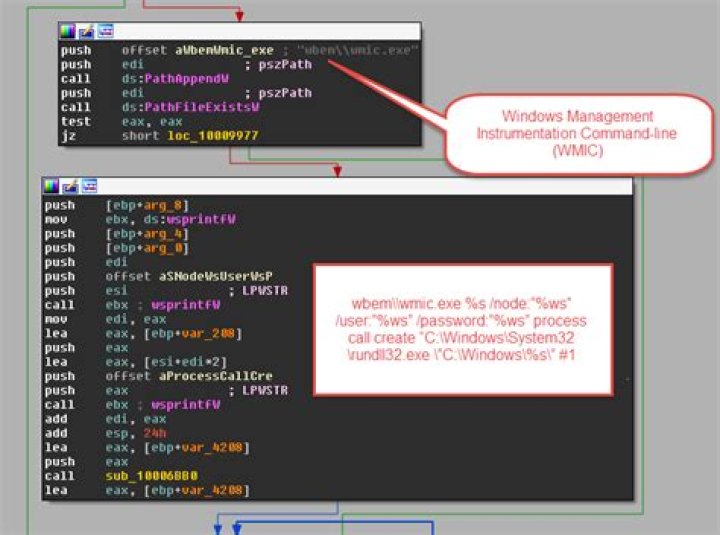
Browser hijackers are generally pretty very easy to remove. For the most part, they have an independent app that can be spotted in the list of installed software. Due to the specific distribution way of AD&POP BLOCK hijacker, it can be conveniently tracked and erased manually. Nevertheless, if you got AD&POP BLOCK in the package with a free applications, your personal computer may be contaminated with much more major malware – trojans, spyware and even ransomware. That’s why I’d suggest you make use of anti-malware programs to remove the AD&POP BLOCK PUA and all other malware.
You can utilize Microsoft Defender2 – it is capable of discovering and removing a wide range of malware, including mentioned hijacker. Nevertheless, significant malware, that might be present on your computer in the specified instance, can disable the Windows antivirus program by modifying the Group Policies. To stay clear of such scenarios, it is far better to use GridinSoft Anti-Malware.
Download GridinSoft Anti-MalwareTo detect and eliminate all malicious applications on your computer with GridinSoft Anti-Malware, it’s better to use Standard or Full scan. Quick Scan is not able to find all the malware, because it scans only the most popular registry entries and folders.
You can spectate the detected malicious apps sorted by their possible harm during the scan process. But to choose any actions against malicious programs, you need to hold on until the scan is over, or to stop the scan.
To set the action for every spotted virus or unwanted program, click the arrow in front of the name of the detected malicious program. By default, all malware will be moved to quarantine.
Reset browser settings to original ones
To reset your browser settings, you are required to use the Reset Browser Settings option. This action cannot be counteracted by any malware, hence, you will surely see the result. This option can be found in the Tools tab.
After choosing the Reset Browser Settings option, the menu will be shown, where you can choose, which settings will be reverted to the original.
Deleteing AD&POP BLOCK hijacker manually
Besides using anti-malware software for browser restoration, you may choose the “Reset browser settings” function, which is usually embedded in all popular browsers.
- Open “Settings and more” tab in upper right corner, then find here “Settings” button. In the appeared menu, choose “Reset settings” option :
- After picking the Reset Settings option, you will see the following menu, stating about the settings which will be reverted to original :
- Open Menu tab (three strips in upper right corner) and click the “Help” button. In the appeared menu choose “troubleshooting information” :
- In the next screen, find the “Refresh Firefox” option :
After choosing this option, you will see the next message :
- Open Settings tab, find the “Advanced” button. In the extended tab choose the “Reset and clean up” button :
- In the appeared list, click on the “Restore settings to their original defaults” :
- Finally, you will see the window, where you can see all the settings which will be reset to default :
- Open Settings menu by pressing the gear icon in the toolbar (left side of the browser window), then click “Advanced” option, and choose “Browser” button in the drop-down list. Scroll down, to the bottom of the settings menu. Find there “Restore settings to their original defaults” option :
- After clicking the “Restore settings…” button, you will see the window, where all settings, which will be reset, are shown :
As an afterword, I want to say that time plays against you and your PC. The activity of browser hijacker must be stopped as soon as possible, because of the possibility of other malware injection. This malware can be downloaded autonomously, or offered for you to download in one of the windows with advertisements, which are shown to you by the hijacker. You need to act as fast as you can.
References
- More information about PUAs
- Detailed review of Microsoft Defender