Trojan:Win32/Casdet!rfn

Sarah Oconnell
Updated on March 28, 2026
What is Trojan:Win32/Casdet!rfn infection?
In this post you will certainly discover about the definition of Trojan:Win32/Casdet!rfn and also its unfavorable influence on your computer. This virus can correctly be classified as hacktool – a program which is designed and used to break different security elements of an operating system.
In the majority of the instances, Trojan:Win32/Occamy.C hacktool will not show any signs of its presence. However, the user may notice the changes of the components he uses everyday, because it is impossible for this virus to make everything quiet.
Trojan:Win32/Casdet!rfn Summary
These modifications can be as complies with:
- Executable code extraction. Cybercriminals often use binary packers to hinder the malicious code from reverse-engineered by malware analysts. A packer is a tool that compresses, encrypts, and modifies a malicious file’s format. Sometimes packers can be used for legitimate ends, for example, to protect a program against cracking or copying.
- Injection (inter-process);
- Injection (Process Hollowing);
- Creates RWX memory. There is a security trick with memory regions that allows an attacker to fill a buffer with a shellcode and then execute it. Filling a buffer with shellcode isn’t a big deal, it’s just data. The problem arises when the attacker is able to control the instruction pointer (EIP), usually by corrupting a function’s stack frame using a stack-based buffer overflow, and then changing the flow of execution by assigning this pointer to the address of the shellcode.
- HTTP traffic contains suspicious features which may be indicative of malware related traffic;
- Performs some HTTP requests;
- The binary likely contains encrypted or compressed data. In this case, encryption is a way of hiding virus’ code from antiviruses and virus’ analysts.
- Executed a process and injected code into it, probably while unpacking;
- Checks for the presence of known windows from debuggers and forensic tools;
- Steals private information from local Internet browsers;
- Network activity contains more than one unique useragent.;
- Collects information about installed applications;
- Checks the CPU name from registry, possibly for anti-virtualization;
- Harvests credentials from local FTP client softwares;
- Harvests information related to installed instant messenger clients;
- Collects information to fingerprint the system. There are behavioral human characteristics that can be used to digitally identify a person to grant access to systems, devices, or data. Unlike passwords and verification codes, fingerprints are fundamental parts of user’s identities. Among the threats blocked on biometric data processing and storage systems is spyware, the malware used in phishing attacks (mostly spyware downloaders and droppers), ransomware, and Banking Trojans as posing the greatest danger.
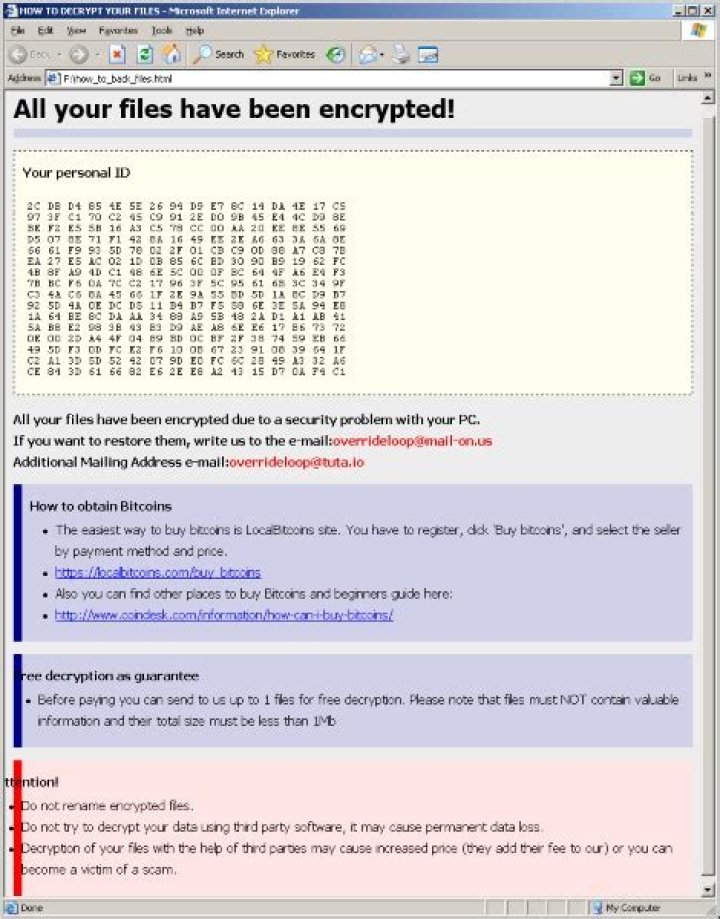
| klegrandlichgrum.com | Trojan-Ransom.GandCrab |
| ip-api.com | Trojan-Ransom.GandCrab |
How Trojan:Win32/Casdet!rfn is distributed?
The majority of cases of Trojan:Win32/Casdet!rfn malware delivery goes to these ways:
Malicious advertisements on the web, however, is an old-timer of malware distribution. And the advice to stop clicking the blinking advertisements on untrustworthy websites exists as long as the ads on the Internet. You can also install ad blocking plugins for your web browser – they will deal with any kind of ads. However, if they are generated by adware which is already present on your PC, ad blockers will be useless.
Email spamming became a very popular malware distribution method, since the users do not raise suspicion on notifications from DHL or Amazon about the incoming delivery. However, it is quite easy to distinguish the malevolent email from the original one. One which is send by a cybercriminals has a strange sender address – something like , while the original email address has a specific domain name (@amazon.com or @dhl.us) and can also be seen on the official website in the “Contact us” tab.
Software bundling is a widespread practice among the virus developers. Users who hack the programs to make them usable without purchasing a license approve any offer to include another program to the pack, because they are gaining money in such a way. Check precisely the installation window for signs like “Advanced installation settings” or so. The ability to switch off the malware installation often hides under such items.
How can I detect that my PC is infected with Trojan:Win32/Casdet!rfn virus?
In different edges of the world, victims of the Trojan:Win32/Casdet!rfn say about different signs of virus activity. Nonetheless, the common sign of the fact that your PC was attacked by a hacktool is disabling the security mechanisms (passwords) in the major system elements.
Changes that are made by Trojan:Win32/Casdet!rfn virus are next:
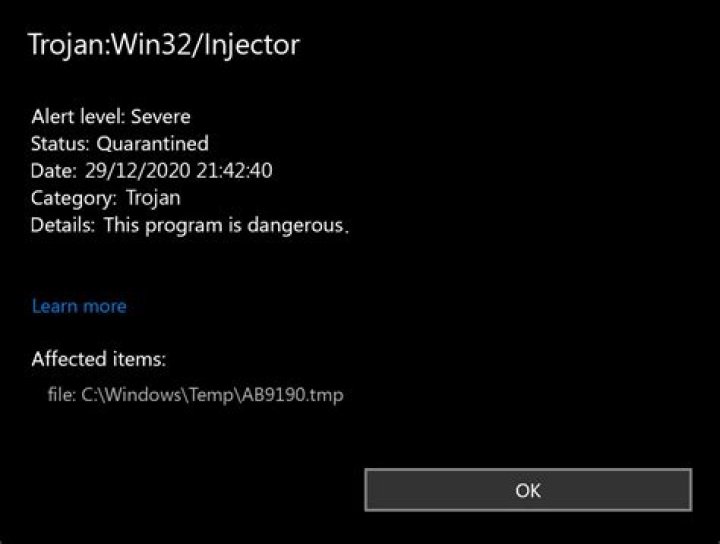
Disabling the Windows Defender. An embedded anti-malware solution from Microsoft is a favorite target of malware creators. And since it is so easy to disable through Group Policies, every second trojan virus makes this action. XXXXXXXXXX is not an exception. After that step, you will not get a notification about the detected malware.
Making several complicated manipulations with the system security settings. The virus disables not only a visible security mechanism but also turns off the methods which are used by the system to prevent malware execution. Under this term I mean the forbid to launch the VBS scripts, disabled by default MS Office macroses or remote registry editing facilities.
Password extraction. Users who make use of a local Windows account may lose their credentials. The password of the local account is stored in a separate area of the winlogon process in encrypted form. Virus may easily call the decrypt function, and get the password of your account, as well as passwords of all users of your PC and local network.
Technical details
File Info:
crc32: BB067C54md5: c3defbd7fffd387d09be5347ec1a83a1name: dor.exesha1: ebc54f115ef8f632c6b46e72fddab8c9ba383ff3sha256: 189464e30cbebaec6a543baaf35c24a2d0f44143fc6992014c81780563c0984asha512: 1796986c67528a0d02149abee0f1548551db6708cdf8affd79b3019a30c66fdf37b11abd19e4b0c055b88d1f8caa6c316cf27f96466bb59672415f120f492383ssdeep: 24576:E8DmVchRKPN6ESo+0JB2XIweCpI9Z2UBfVYhzZFQ4mB6tQJ:gARKPN6ESz0nw5pI9ZTfVIXQAqJtype: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
LegalCopyright: Copyright xa9 2000 - 2014 KG and its LicensorsInternalName: Mrale DetectableFileVersion: 5.7.4.7CompanyName: NoVirusThanks Company SrlLegalTrademarks: Copyright xa9 2000 - 2014 KG and its LicensorsComments: Sculatr 2500 AesProductName: Mrale DetectableProductVersion: 5.7.4.7FileDescription: Sculatr 2500 AesTranslation: 0x0409 0x04b0
Trojan:Win32/Casdet!rfn also known as:
| GridinSoft | Trojan.Ransom.Gen |
| MicroWorld-eScan | Trojan.GenericKD.41899419 |
| FireEye | Generic.mg.c3defbd7fffd387d |
| CAT-QuickHeal | Trojan.Chapak |
| McAfee | Artemis!C3DEFBD7FFFD |
| Malwarebytes | Spyware.Vidar |
| Zillya | Trojan.Kryptik.Win32.1794435 |
| Sangfor | Malware |
| K7AntiVirus | Trojan ( 00559c111 ) |
| Alibaba | Trojan:Win32/Chapak.d8c8bbfe |
| K7GW | Trojan ( 00559c111 ) |
| CrowdStrike | win/malicious_confidence_90% (W) |
| Invincea | heuristic |
| BitDefenderTheta | Gen:NN.ZexaF.32519.mz0@aSC2ukhi |
| Symantec | Trojan.Gen.MBT |
| APEX | Malicious |
| Avast | Win32:Malware-gen |
| GData | Trojan.GenericKD.41899419 |
| Kaspersky | Trojan.Win32.Chapak.eatw |
| BitDefender | Trojan.GenericKD.41899419 |
| NANO-Antivirus | Trojan.Win32.Chapak.gdndpe |
| AegisLab | Trojan.Multi.Generic.4!c |
| Rising | Trojan.Generic@ML.83 (RDML:xkjjshEts+8//lcMJjLh/g) |
| Endgame | malicious (high confidence) |
| Sophos | Mal/Generic-S |
| Comodo | Malware@#3v13sehq3v075 |
| F-Secure | |
| DrWeb | Trojan.PWS.Stealer.24298 |
| VIPRE | Trojan.Win32.Generic!BT |
| TrendMicro | TROJ_GEN.R020C0WJH19 |
| McAfee-GW-Edition | BehavesLike.Win32.Generic.tc |
| Emsisoft | Trojan.GenericKD.41899419 (B) |
| Ikarus | Trojan-Ransom.GandCrab |
| Cyren | W32/Trojan.DIWJ-1219 |
| Webroot | W32.Chapak.Eatw |
| Avira | TR/AD.MalwareCrypter.qbunp |
| Antiy-AVL | Trojan/Win32.Chapak |
| Microsoft | Trojan:Win32/Casdet!rfn |
| Arcabit | Trojan.Generic.D27F559B |
| ZoneAlarm | Trojan.Win32.Chapak.eatw |
| AhnLab-V3 | Trojan/Win32.Chapak.C3517361 |
| Acronis | suspicious |
| ALYac | Trojan.Agent.Casur |
| MAX | malware (ai score=87) |
| Ad-Aware | Trojan.GenericKD.41899419 |
| Cylance | Unsafe |
| Panda | Trj/CI.A |
| ESET-NOD32 | a variant of Win32/Injector.EIOZ |
| TrendMicro-HouseCall | TROJ_GEN.R020C0WJH19 |
| Fortinet | W32/Chapak.EATW!tr |
| AVG | Win32:Malware-gen |
| Paloalto | generic.ml |
| Qihoo-360 | HEUR/QVM10.2.91A3.Malware.Gen |
How to remove Trojan:Win32/Casdet!rfn virus?
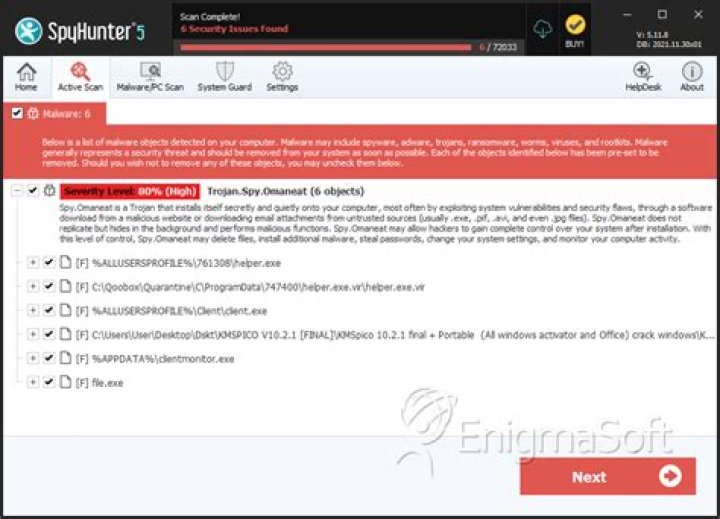
The is an excellent way to deal with recognizing and removing threats – using Gridinsoft Anti-Malware. This program will scan your PC, find and neutralize all suspicious processes.">2.
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
Download GridinSoft Anti-MalwareRun the setup file.
When setup file has finished downloading, double-click on the install-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.
An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.
Press “Install” button.
Once installed, Anti-Malware will automatically run.
Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for Trojan:Win32/Casdet!rfn files and other malicious programs. This process can take a 20-30 minutes, so I suggest you periodically check on the status of the scan process.
Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.
Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offer real-time protection for first 2 days. If you want to be fully protected at all times – I can recommended you to purchase a full version:
Full version of GridinSoft Anti-Malware
If the guide doesn’t help you to remove Trojan:Win32/Casdet!rfn you can always ask me in the comments for getting help.
References
- GridinSoft Anti-Malware Review from HowToFix site:
- More information about GridinSoft products: