Trojan:Script/Phonzy.B!ml

Olivia Norman
Updated on April 03, 2026
What is Trojan:Script/Phonzy.B!ml infection?
In this post you will certainly locate regarding the interpretation of Trojan:Script/Phonzy.B!ml and its negative influence on your computer. That trojan virus may be correctly classified as trojan-downloader. You will see the information about that virus type below.
In the majority of the situations, Trojan:Script/Phonzy.B!ml virus will not try to show its presence in your system. The more time that virus will be active, the more additional viruses it will bring into your system.
Trojan:Script/Phonzy.B!ml Summary
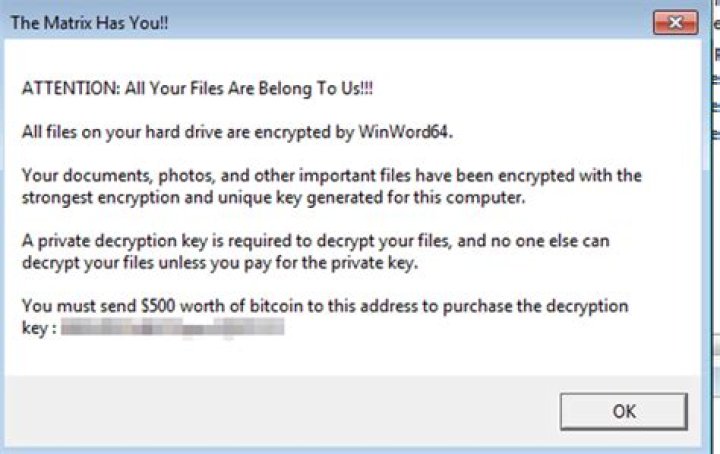
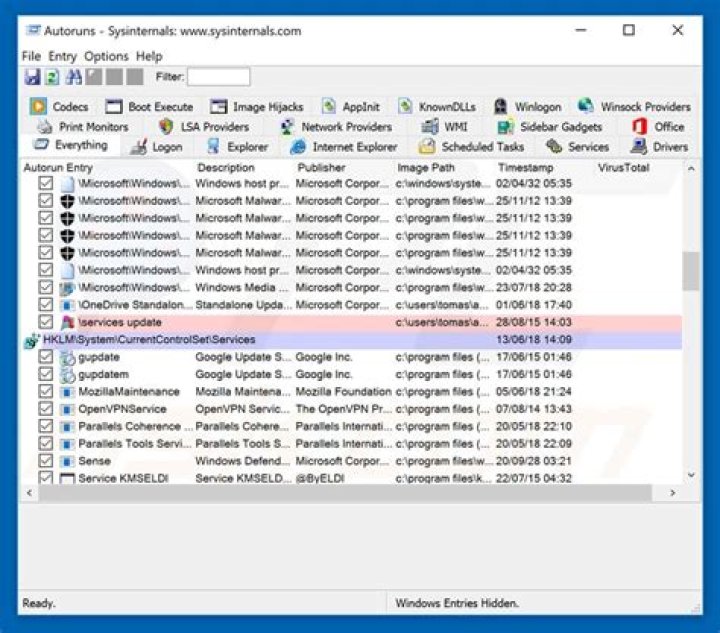
As it was mentioned, Trojan:Script/Phonzy.B!ml acts as a downloader for other viruses, preparing the “comfortable” environment for the arriving malware. It makes changes in various system configurations. Usually, units under attack are networking settings and Microsoft Defender. Changing the networking settings can lead to problems with connecting to some websites or servers. Disabling the Windows Defender is much easier to discover, but a lot of users do not use this antivirus tool. Hence, the chance that the virus activity will stay undetected until the additional malware is downloaded is very high.
How did Trojan:Script/Phonzy.B!ml infiltrated into my PC?
These days, viruses are distributed in tens of different ways. However, such malware as Phonzy is usually spread through email spamming, questionable programs and bundled software. Doubtful programs are spread as some sort of specific tools. Programs like KMSPico are used as activators for Windows, that allow you to use the system without purchasing the license. Viruses can be downloaded instead of the offered program, or even as a part of legit apps. You may use that tool without a thought about the malicious activity undercover. Trojan:Script/Phonzy.B!ml virus can be spread together with the system optimizers or driver updaters.
Software bundling is a widespread practice among the virus developers. Users who hack the programs to make them usable without purchasing a license approve any offer to include another program to the pack, because they are gaining money in such a way. Check precisely the installation window for signs like “Advanced installation settings” or so. The ability to switch off the malware installation often hides under such items.
The example of bundle software installation
Email spamming is a very popular malware distribution method, since the users do not raise suspicion on notifications from DHL or Amazon about the incoming delivery. However, it is quite easy to distinguish the malevolent email from the original one. One which is send by a cybercriminals has a strange sender address – something like , while the original email address has a specific domain name (@amazon.com or @dhl.us) and can also be seen on the official website in the “Contact us” tab.
How can I understand that my computer is infected with Trojan:Script/Phonzy.B!ml?
In different edges of the world, victims of the Trojan:Script/Phonzy.B!ml? say about different signs of virus activity. Nonetheless, the common sign of the fact that you PC was infected by a trojan-downloader is a tremendous slowdown of your system. It is very hard to miss that moment, because even the most powerful PCs become slow as snails when 3-5 viruses begin working simultaneously.
As I mentioned before, Trojan:Script/Phonzy.B!ml? downloader makes several changes to the system configurations. It disables the Microsoft Defender – the embedded anti-malware solution for Windows. A lot of users do not make use of third-party antivirus programs because of the Defender availability. But the fact that it can be disabled in several clicks through the Group Policies settings creates a big risk. If you see that Defender stopped working without your command, it is not OK. Scan your system with GridinSoft Anti-Malware – you will likely find a malicious item which stopped the embedded antivirus.
Technical details
File Info:
crc32: 28672805md5: 09193216c7f9523db3ada5c83d5d18c2name: 09193216C7F9523DB3ADA5C83D5D18C2.mlwsha1: d0e658d31c35184416410afcde94c03581da1cafsha256: a731471863bb047e28e94c7d8c058bc0212d773b461ec605ac6f3bc9b6df6727sha512: d863acf21e168c17b4f2e1c60cd0605f0653fa4c91a71ab4ab369d00d8b5a19d2d8cc7cff30267a589ed61ac32edfd54b46b854da41dfda62689c1ee854f8e18ssdeep: 12288:4y53BGnmCZJ166xGpw2tYuPVF6LN59qqURafTvMvd9al7jOoCIliWP6c3mi4bmb:4GkHpxCw2uwi9qqURS+d9S7vDiWPl3Ytype: PE32 executable (console) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressedVersion Info:
0: [No Data]
Trojan:Script/Phonzy.B!ml also known as:
| GridinSoft | Trojan.Ransom.Gen |
| Bkav | W32.AIDetect.malware1 |
| K7AntiVirus | Trojan ( 0057792a1 ) |
| Elastic | malicious (high confidence) |
| Cynet | Malicious (score: 100) |
| ALYac | Trojan.GenericKD.36662186 |
| Sangfor | Trojan.Script.Phonzy.A |
| CrowdStrike | win/malicious_confidence_90% (W) |
| Symantec | Trojan.Gen.MBT |
| Avast | Win32:Trojan-gen |
| BitDefender | Trojan.GenericKD.36662186 |
| NANO-Antivirus | Trojan.Win32.RanumBot.ieldot |
| MicroWorld-eScan | Trojan.GenericKD.36662186 |
| Ad-Aware | Trojan.GenericKD.36662186 |
| Sophos | Mal/Generic-S |
| McAfee-GW-Edition | BehavesLike.Win32.VirRansom.jc |
| FireEye | Trojan.GenericKD.36662186 |
| Emsisoft | Trojan.GenericKD.36662186 (B) |
| SentinelOne | Static AI – Suspicious PE |
| Microsoft | Trojan:Script/Phonzy.B!ml |
| AegisLab | Trojan.Win32.Generic.4!c |
| GData | Trojan.GenericKD.36662186 |
| McAfee | GenericRXAA-FA!09193216C7F9 |
| MAX | malware (ai score=89) |
| Malwarebytes | Malware.AI.4278635530 |
| Rising | Malware.Heuristic!ET#94% (RDMK:cmRtazogYpcLL772VwUAA04SPWEo) |
| MaxSecure | Trojan.Malware.111454061.susgen |
| Fortinet | W32/RanumBot.Y!tr |
| AVG | Win32:Trojan-gen |
How to remove Trojan:Script/Phonzy.B!ml virus?
There is no better way to recognize, remove and prevent PC threats than to use an anti-malware software from GridinSoft">2.
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
Download GridinSoft Anti-MalwareRun the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.
An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.
Press “Install” button.
Once installed, Anti-Malware will automatically run.
Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for Trojan:Script/Phonzy.B!ml files and other malicious programs. This process can take a 20-30 minutes, so I suggest you periodically check on the status of the scan process.
Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.
Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offer real-time protection for first 2 days. If you want to be fully protected at all times – I can recommended you to purchase a full version:
Full version of GridinSoft Anti-Malware
If the guide doesn’t help you to remove Trojan:Script/Phonzy.B!ml you can always ask me in the comments for getting help.
References
- GridinSoft Anti-Malware Review from HowToFix site:
- More information about GridinSoft products: