Trojan:Script/Phonzy.A!ml

Emily Beck
Updated on March 10, 2026
What is Trojan:Script/Phonzy.A!ml infection?
In this short article you will certainly locate regarding the definition of Trojan:Script/Phonzy.A!ml and also its negative influence on your computer. This trojan virus is used to steal your banking credentials. That malware type is also called banking trojans.
It is better to prevent, than repair and repent!
When we talk about the intrusion of unfamiliar programs into your computer’s work, the proverb “Forewarned is forearmed” describes the situation as accurately as possible. Gridinsoft Anti-Malware is exactly the tool that is always useful to have in your armory: fast, efficient, up-to-date. It is appropriate to use it as an emergency help at the slightest suspicion of infection.EULA | Privacy Policy | Gridinsoft
Most of the cases, Trojan:Script/Phonzy.A!ml infection will show no easy-to-spot signs of its presence, but a close look will be enough to see the results of its activity.
Trojan:Script/Phonzy.A!ml Summary
This virus can be identified as a banking trojan. That virus type if close to trojan-stealers – trojans that aim on your credentials and sensitive data. Banking trojans became extremely widespread after the appearance of online banking as a service. Its name clearly says that trojan targets your banking account credentials. Every bank has its own security mechanisms, which are designed to prevent the attempt to steal the credentials from the login window. That’s why banking trojans have a lot of facilities to detour these security layers.
Phonzy trojan can try to steal your login data in different ways. Some banks that do not have any anti-stealer protection on their online banking pages, so the virus can do nothing. All he needs is to copy the login and password you typed and keep them in the separate file. Then, virus sends that file to its command server. Banks who care about the security of their customers do not allow the virus to steal the data so easily. Trojan:Script/Phonzy.A!ml changes your networking settings, as well as browser configurations. When the virus understands that victim uses the secured online banking website, it manages to show you the phishing page which mimics the original banking page. Phonzy makes that trick through the HOSTS file change. When you try to open the online banking website, you will see a well-designed counterfeit. In fact, that page has only a login window and a login error popup.
Trojan:Script/Phonzy.A!ml injection ways
Trojan:Script/Phonzy.A!ml virus has quite a new distribution model. It is usually spread as a component of the software, that looks like 100% legit and has all declared functions. That’s why it has a “Script” in the detection name. The ability to be embedded into the program makes this virus extremely flexible – all you need is to have access to the source code of the program you want to be a carrier for the malware. And the virus creators have no need to create their own software to use it as a basic app. They can offer to include their “add-on” into the freeware or hacked program (i.e. one which license checking is disabled) for a substantial payment. The developers of free software are always glad to get such offers, and accept them regardless of the goodness of the offered addition.
Trojan:Script/Phonzy.A!ml visible effects.
As it was mentioned, Trojan:Script/Phonzy.A!ml acts as a banking trojan, stealing the login information from your online banking account. Changing the networking settings can lead to problems with connecting to some websites or servers. Disabling the Windows Defender is much easier to discover, but a lot of users do not use this antivirus tool. Hence, the chance that the virus activity will stay undetected until it is too late is very high. The less time is passed after the virus injection – the less the chance of bad consequences. Remove the virus with the guide below.
Technical details
File Info:
crc32: 4A2A7092md5: 177e3c8c5cecc77f98bf6f8e601119a2name: 177E3C8C5CECC77F98BF6F8E601119A2.mlwsha1: 7037486f99c7854690d7b3fbc352c42494fe75besha256: 45f883446e39c9d0e969c27d09b8e9877d901a75aeaf443a67715274a4f86af4sha512: 24bc4616e13733eb744e30ceed76cb6bc346de01fc81041a80be7f9f03fd5bc49f1a9f9670ebdf2bfe061bc9d1581ba4c1e3f1a5c64ed01799a712d221d1f135ssdeep: 24576:jFhbBMXmUcI2AqOvVuK5zmfOUyxCHjwKTJuN6:JUmu2AjCH0KTUNtype: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
0: [No Data]
Trojan:Script/Phonzy.A!ml also known as:
| GridinSoft | Trojan.Ransom.Gen |
| Elastic | malicious (high confidence) |
| MicroWorld-eScan | Gen:Variant.Zusy.342026 |
| FireEye | Generic.mg.177e3c8c5cecc77f |
| CAT-QuickHeal | Ransom.PornoBlocker.14190 |
| ALYac | Gen:Variant.Zusy.342026 |
| Cylance | Unsafe |
| Zillya | Trojan.Agent.Win32.192947 |
| AegisLab | Trojan.Win32.Injector.togd |
| K7AntiVirus | Riskware ( 0040eff71 ) |
| BitDefender | Gen:Variant.Zusy.342026 |
| K7GW | Riskware ( 0040eff71 ) |
| Cybereason | malicious.c5cecc |
| BitDefenderTheta | Gen:NN.ZexaF.34804.WyW@amTzJZpi |
| Cyren | W32/Trojan.YNQR-4209 |
| Symantec | ML.Attribute.HighConfidence |
| APEX | Malicious |
| Avast | Win32:Evo-gen [Susp] |
| Alibaba | Trojan:Win32/WrongInf.2f8c0b42 |
| NANO-Antivirus | Trojan.Win32.Zusy.hbwqhv |
| Rising | Trojan.Generic@ML.90 (RDML:j4OIwc+jUpZZZoRrc2sN/A) |
| Ad-Aware | Gen:Variant.Zusy.342026 |
| TACHYON | Trojan/W32.PornoBlocker.794624 |
| Sophos | Mal/Generic-S |
| DrWeb | Trojan.MulDrop.59624 |
| VIPRE | Trojan.Win32.Generic!BT |
| TrendMicro | TROJ_GEN.R002C0PAR21 |
| McAfee-GW-Edition | BehavesLike.Win32.Generic.bh |
| Emsisoft | Gen:Variant.Zusy.342026 (B) |
| Antiy-AVL | Worm/Win32.Qvod |
| Microsoft | Trojan:Script/Phonzy.A!ml |
| Arcabit | Trojan.Zusy.D5380A |
| SUPERAntiSpyware | |
| GData | Gen:Variant.Zusy.342026 |
| Cynet | Malicious (score: 100) |
| Acronis | suspicious |
| McAfee | GenericRXAQ-ZI!177E3C8C5CEC |
| MAX | malware (ai score=80) |
| VBA32 | TrojanDropper.Injector |
| Malwarebytes | Malware.Heuristic.1001 |
| Panda | Trj/CI.A |
| TrendMicro-HouseCall | TROJ_GEN.R002C0PAR21 |
| Tencent | Malware.Win32.Gencirc.10b63e05 |
| Yandex | Trojan.PornoBlocker!CeY9R2xFhfc |
| SentinelOne | Static AI – Suspicious PE |
| Fortinet | W32/GenericRXAQ.ZI!tr |
| AVG | Win32:Evo-gen [Susp] |
| Paloalto | generic.ml |
| CrowdStrike | win/malicious_confidence_100% (W) |
How to remove Trojan:Script/Phonzy.A!ml virus?
The is an excellent way to deal with recognizing and removing threats – using Gridinsoft Anti-Malware. This program will scan your PC, find and neutralize all suspicious processes.">2.
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
Download GridinSoft Anti-MalwareRun the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.
An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.
Press “Install” button.
Once installed, Anti-Malware will automatically run.
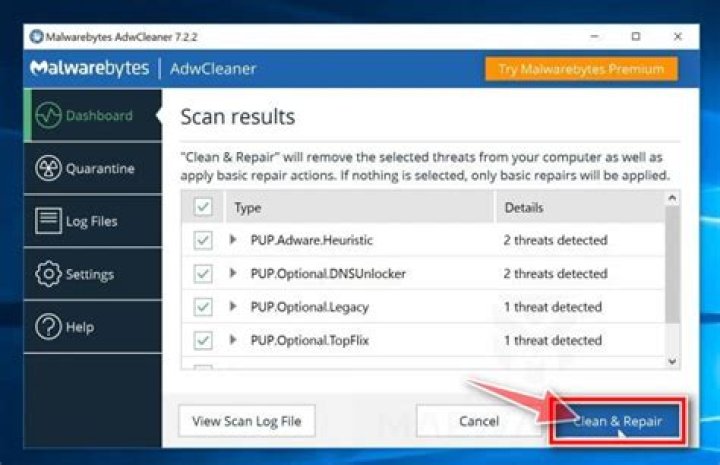
Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for Trojan:Script/Phonzy.A!ml files and other malicious programs. This process can take a 20-30 minutes, so I suggest you periodically check on the status of the scan process.
Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.
Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offer real-time protection for first 2 days. If you want to be fully protected at all times – I can recommended you to purchase a full version:
Full version of GridinSoft Anti-Malware
If the guide doesn’t help you to remove Trojan:Script/Phonzy.A!ml you can always ask me in the comments for getting help.
References
- GridinSoft Anti-Malware Review from HowToFix site:
- More information about GridinSoft products: