Information security specialists discovered attacks on a critical vulnerability in VMware vCenter

Emily Beck
Updated on March 25, 2026
Experts warned that cybercriminals are already actively scanning the network in search of VMware vCenter servers with critical vulnerabilities. Many are at risk of the recently corrected RCE issue CVE-2021-21985, which scored 9.8 out of 10 on the CVSS v3 vulnerability rating scale.
Analysts from Bad Packets write about the scans that have begun.According to the search engine Shodan, there are currently several thousands of vulnerable vCenter servers on the network. And it is necessary to understand that this product is not used by individuals and even small businesses, that is, we are talking about large companies and organizations.
As a reminder, the CVE-2021-21985 issue was detected in the Virtual SAN Health Check plugin included by default with vCenter. An attacker can use this bug to run whatever they want on a vulnerable host (if they have access to port 443). That is, unauthenticated attackers can exploit the problem, and such attacks do not require any interaction with the user.
Even worse, exploits for this bug have already been published online.
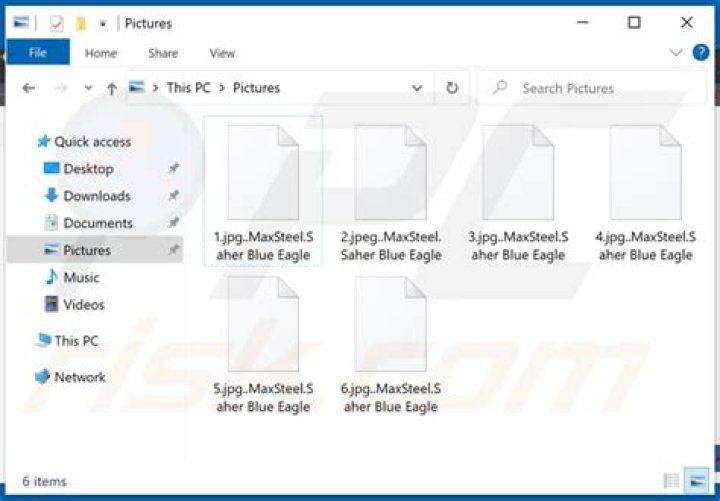
Since such vulnerabilities have been used more than once in the past for destructive attacks (usually ransomware) against large companies, VMware representatives issued an official warning to their customers. In a statement, the company calls for timely installation of updates, as well as beware of ransomware attacks:
Let me remind you that we already reported that VMware Alerts That Critical Vulnerability Has Been Found In vCenter Server.